-
Get a Personalized Demo
- Soluciones
-
Servicios Empresariales
Estrategia de Nube Seguridad Cibernética Servicios Administrados Gestión de Socios Servicios de Portación
- Industrias
-
Industries We Serve
- Conocimientos
-
Recursos
Eventos
Ready to learn more about IAG now?
Watch our on-demand video on how identity management is
done in a typical organization.
- Carreras
-
We’re constantly on the hunt for talented individuals who are passionate about innovative technologies
- Socios
-
Socios
Partner Program
- Compañia
-
GLOBAL
Sobre ISSQUARED -
IN INDIA
ISSQUARED
- Book a Demo
-
Book a Demo
Fabulix Service Manage (FSM)
-
- Español
- العربية
- Français
- English
- Dutch
Thank you for your interest. We Will Contact You Soon...Your email ID is already registered with us.Check Out Our On-demand
Live StreamsShow Introduction and Security Trends
Watch VideoSecuring Active Directory
Watch Video
NextGen SIEM – staying ahead of the game
Watch VideoSecuring APIs – Next Perimeter
Watch Video
NextGen SIEM – Deep Dive
Watch Video

Managing Cyber Security Risk
Watch Video

Zero Trust and Passwordless Authentication
Watch Video
Zero Trust Part - I
Watch Video
Zero Trust Part - II
Watch Video
Authentication and Zero Trust | Part - I
Watch Video
Authentication and Zero Trust | Part - ||
Watch Video
Cyber Insurance – Part I
Watch Video
Cyber Insurance – Part II
Watch Video
Deception: Part - I
Watch Video
Deception: Part - II
Watch Video
Zero Trust in the Clouds: Part - I
Watch Video
Zero Trust in the Clouds: Part II
Watch Video
Unpacking National Cybersecurity Strategy - I
Watch Video
Unpacking National Cybersecurity Strategy - II
Watch Video
Unpacking National Cybersecurity Strategy - III
Watch Video
Lessons in Leadership: From Finance to Cyber Security - Part I
Watch Video
Lessons in Leadership: From Finance to Cyber Security - Part II
Watch Video
Lessons in Leadership: From Finance to Cyber Security - Part III
Watch Video
Building Cybersecurity Strategy
Watch Video
Building Cybersecurity Strategy - Part II
Watch Video
What is Lurking in Those Chips? - Part I
Watch Video
What is Lurking in Those Chips? - Part II
Watch Video
What is Lurking in Those Chips? - Part III
Watch Video
Threat Landscape - Part I
Watch Video
Threat Landscape - Part II
Watch Video
Threat Landscape - Part III
Watch Video
Diving Deep into Incident Response - Part I
Watch Video
Diving Deep into Incident Response - Part II
Watch Video
LockBit: Tactics, Technics, and Misdeeds : Part - I
Watch Video
LockBit: Tactics, Technics, and Misdeeds : Part - II
Watch Video
Cybersecurity Judgement Day: Part - I
Watch Video
Cybersecurity Judgement Day: Part - II
Watch Video
When Response is Not An Option: Part - I
Watch Video
Leadership and Humility in Cyber: Part - I
Watch Video
Leadership and Humility in Cyber: Part - II
Watch Video
Cybersecurity and Geopolitics: Part - I
Watch Video
Cybersecurity and Geopolitics: Part - II
Watch Video
Road To A CISO Role: Part - I
Watch Video
Road To A CISO Role: Part - II
Watch Video
Making Sense in Compliance
Watch Video
Making Sense in Compliance: Part - II
Watch Video
Cybersecurity and Geopolitics: Part - I
Watch Video
Cybersecurity and Geopolitics: Part - II
Watch Video
The Rise of the Machines: Part - I
Watch Video
The Rise of the Machines: Part - II
Watch Video
Active Directory: Part - l
Watch Video
Active Directory: Part - ll
Watch Video
TYPHOONS ARE COMING! : Part - ll
Watch Video
TYPHOONS ARE COMING! : Part - l2
Watch Video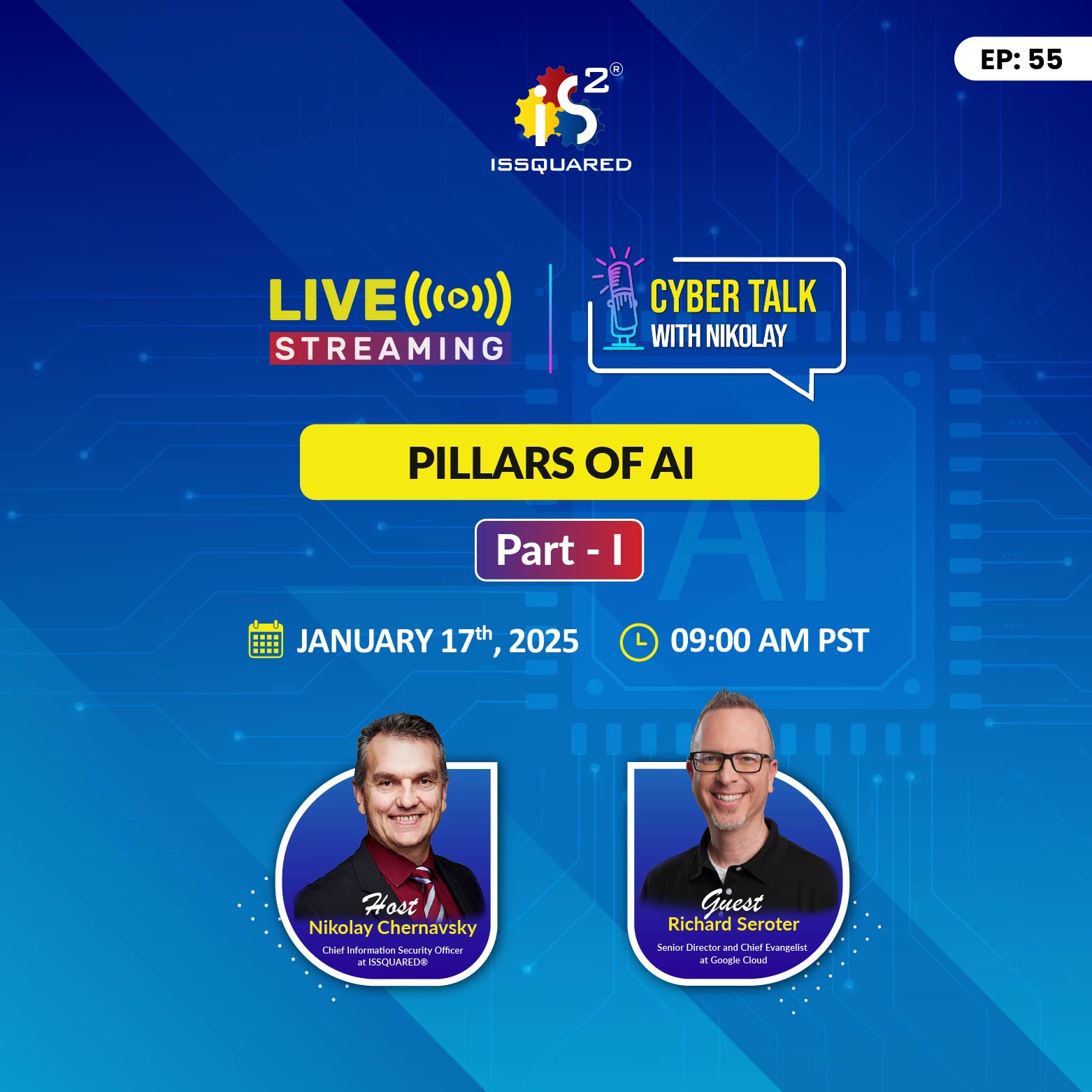
PILLARS OF AI: Part - 1
Watch Video
PILLARS OF AI: Part - 2
Watch Video
What 2025 Holds in the Cyber Store 01
Watch VideoSubscribe to
Cyber Talk with Nikolay
Receive the alert for the new episode, right to your inbox.
This website uses cookies or similar technologies, to enhance your browsing experience and provide personalized recommendations. By continuing to use our website, you agree to our Privacy Policy
Thank you for your interest. We Will Contact You Soon...Your email ID is already registered with us. - Soluciones